
-

Comment un jacuzzi peut-il transformer votre week-end en amoureux en une expérience insolite ?
Détente, relaxation et moments privilégiés à deux sont autant d’ingrédients indispensables pour réussir un week-end en amoureux. Et quoi de mieux qu’un ..
-

Le 12ème arrondissement est-il le meilleur endroit pour passer son permis rapidement ?
Dans la capitale française, obtenir son permis de conduire est un véritable enjeu. Chacun souhaite le passer le plus rapidement possible et sans problème. Est-ce ..
-
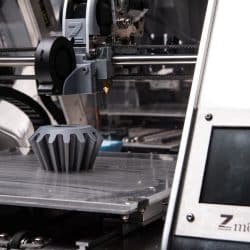
Quelles sont les possibilités offertes par l’impression 3D grand format ?
L’impression 3D est une technologie en plein essor depuis quelques années, et le secteur du grand format n’est pas en reste. Grâce à cette méthode ..
-

Qui contacter pour avoir une location d’un camion à La Rochelle ?
Plusieurs moyens de transport existent et leur utilité dépend de l’utilisation que l’on veut en faire. Que vous prévoyez de déménager, d’organiser ..
-

Pourquoi et comment roder vos nouvelles plaquettes de frein ?
Le rodage est une étape essentielle lors du remplacement des plaquettes de frein de votre véhicule. Cette procédure permet d’établir une surface de contact ..
-

Comment trouver un cours d’œnologie de qualité à Paris sans dépenser une fortune ?
Trouver un cours d’œnologie de qualité à Paris sans se ruiner peut sembler aussi complexe que de dénicher une bouteille de Grand Cru à prix d’ami. Mais ..
-

Comment changer le liquide de frein de votre véhicule étape par étape ?
Changer le liquide de frein de son véhicule est une opération d’entretien essentielle pour garantir la sécurité et l’efficacité du système de freinage. ..
-

Comment utiliser le tableau Montessori pour enrichir l’expérience éducative de votre enfant ?
Le tableau Montessori est un outil d’éducation exceptionnel pour enrichir l’expérience éducative des enfants. Il favorise leur développement global ..
-

Faut-il un visa pour danser la salsa sous le soleil de Cuba ?
Vous êtes en train de préparer votre valise pour une aventure cubaine et soudain, la question se pose : est-il nécessaire d’avoir un visa pour Cuba ? Ah, les joies ..
-

Comment une suspension boule en verre peut-elle réinventer votre espace ?
La suspension boule en verre design est un magnifique objet, n’est-ce pas ? Je me suis toujours demandé comment un simple luminaire pouvait totalement transformer ..
-

Peut-on réellement obtenir un prêt rapide sans justificatif ?
Dans certaines situations, comme la perte d’un emploi, des frais médicaux imprévus ou une dépense urgente pour réparer son domicile, on peut avoir besoin ..
-

Comment lancer une franchise burger en France type fast food ?
Le marché de la restauration rapide en France est en constante évolution, attirant un grand nombre d’entrepreneurs souhaitant se lancer dans ce secteur dynamique. ..
-

Comment entretenir un aspirateur sans sac Miele ?
Les aspirateurs sans sac Miele sont réputés pour leur performance, leur durabilité et leur facilité d’utilisation. Pour garantir un fonctionnement optimal ..
-

Comment s’assurer contre la fraude bancaire?
La fraude bancaire est un problème croissant qui touche de nombreux consommateurs chaque année. Dans le monde bancaire d’aujourd’hui, la question de l’assurance ..
-

Que faire en cas de panne de serveur ?
Les pannes de serveurs peuvent causer des problèmes majeurs pour les entreprises et les particuliers. Il est essentiel d’être bien préparé et de savoir ..
-

Comment personnaliser un semainier ?
Avoir un agenda personnalisé, adapté à ses besoins et à son goût est l’idéal pour optimiser son temps et rester organisé. Voici quelques idées et techniques ..
-

Pourquoi c’est important d’avoir un bon casque quand on travaille dans un centre d’appel ?
Dans un centre d’appel, le casque est l’outil de travail principal des conseillers. Il permet à la fois de communiquer avec les clients et les collègues, ..
-

Comment louer un ordinateur portable en tant que particulier ?
Il peut y avoir de nombreuses raisons qui vous poussent à ne pas vouloir investir dans un ordinateur portable. Vous pouvez en avoir besoin de manière très occasionnelle ..
-

Comment utiliser la télécommande de la barre de son Samsung ?
Si vous aimez profiter d’une qualité toujours optimale pour regarder vos films, vos séries, ou encore jouer aux jeux vidéo, il va falloir bien vous équiper. ..
-

Qu’est-ce qui distingue la barre de son Samsung des autres ?
La barre de son est un équipement à la pointe de la technologie, qui fait aujourd’hui partie des indispensables au moment d’équiper votre salon. Son rôle ..
-

Comment booster sa sexualité avec un vibromasseur clitoridien ?
Le vibromasseur clitoridien est un jouet sexuel conçu spécifiquement pour stimuler le clitoris, la zone érogène la plus sensible de la femme. Ce style de sextoy ..
-

Que signifient les lignes sur le marquage au sol du code de la route ?
Lorsque vous préparez l’examen théorique, vous devez impérativement vous focaliser sur tous les domaines les plus problématiques. Ils sont souvent la cible ..
-

Quel type de coupe-vent est le plus adapté pour le foot ?
Quand on aime le sport, il y a de nombreux équipements et vêtements indispensables pour pratiquer dans les bonnes conditions. Particulièrement quand on fait un sport ..
-
Quels sont les meilleures plateformes de mission pour développeur en freelance ?
Le développement web est inséparable avec la publication des sites Internet performants proposés aux Internautes en ligne. C’est pourquoi une entreprise œuvrant ..
-

Comment trouver un chirurgien spécialisé en augmentation mammaire sur Paris ?
Si vous envisagez d’avoir recours à la chirurgie pour augmenter le volume de votre poitrine, il est important de prendre le temps de bien choisir le professionnel ..
-

Découvrez les avantages du soutien-gorge brassière avec un excellent maintien pour le sport
Si vous souhaitez vous motiver pour le sport, il va être important de rapidement le pratiquer dans les meilleures conditions possibles. Et cela passe par des tenues ..
-

Comment réserver une chambre à la maternité du CHU Poitiers grâce à Happytal ?
Passer un séjour à l’hôpital n’a rien d’agréable, c’est pourquoi vous devez savoir qu’il existe dès à présent un service vous ..
-

Quelles sont les règles de sécurité pour utiliser un fumigènes lors d’une baby shower ou gender reveal ?
Aujourd’hui, les fumigènes sont de plus en plus sollicités dans les événements festifs, notamment lors d’une baby shower ou gender reveal. Ils sont très ..
-

Dans quelles villes d’Ecosse peut-on envoyer un adolescent faire un séjour linguistique ?
S’il y a bien un endroit où vous pourriez en profiter pour faire un séjour linguistique, c’est bel et bien l’Ecosse ! En effet, alors que de plus ..
-

Quelle couleur de parka pour fille s’accorde avec tous les vêtements ?
Rien ne vous délecterait plus que de vous acheter une nouvelle parka femme pour la période de fin d’année, mais vous êtes une éternelle insatisfaite et ne savez ..
-

Quelle est la différence entre une parka longue et une parka courte pour homme?
En période hivernale, les besoins de se couvrir se font ressentir. Entre manteaux, écharpes, pulls et accessoires, tout est bon pour acheter et réinventer sa garde-robe. ..
-

Comment bien choisir sa guirlande lumineuse extérieure
Pour choisir votre guirlande lumineuse extérieure pour Noël, vous devez d’abord vous baser sur l’usage. En effet, si vous souhaitez créer une ambiance tamisée, ..
-

Quel coffret sport découverte acheter pour offrir un baptême en hélicoptère à un proche ?
Vous avez bientôt un anniversaire qui approche pour l’un de vos proches ou bien pour un membre de votre famille ? Vous avez, au contraire, envie d’anticiper ..
-

Quel site propose la voyance gratuite sans attente par mail ?
Il est toujours intéressant d’avoir une idée sur ce qu’il peut se passer pour nous dans l’avenir, cela permet d’anticiper certaines choses ..
-

Découvrez ces croisières en Antarctique, ces voyages inoubliables au fin fond du monde
L’Antarctique est un contient plein de mystères. Il attire toujours plus les voyageurs et les personnes souhaitant avoir la chance de voir de leurs yeux les paysages ..
-

Quel est le roman policier le plus connu ?
Le roman policier est un genre de fiction qui passionne des millions de lecteurs à travers le monde. Parmi les nombreux titres qui ont été publiés dans ce genre, ..
-
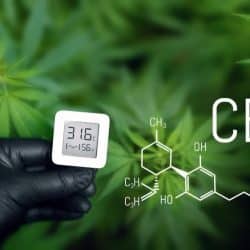
Tout savoir sur les effets psychoactifs du cannabis et les risques de dépendance
La plante de cannabis est composée de cannabinoïdes. Si certains ne présentent pas de risques pour la santé, d’autres peuvent causer des effets néfastes. ..
-

Le CO2 supercritique et son extraction
Solvant neutre, non-toxique, non-polluant et non-inflammable, le CO2 supercritique présente de nombreux avantages. Grâce à ses avantages, il pourrait faire partie ..
-

Nos conseils pour être une excellente femme de ménage
Voici un article présentant les différents conseils à privilégier en vue de devenir un agent d’entretien et de nettoyage recherché. Sollicitées aussi bien ..
-

Comment choisir la meilleure matière pour une couette ?
Pour une nuit de confort dans votre lit, votre couette doit être assez chaude et assez douce, sinon votre sommeil en pâtira. Il y a plusieurs facteurs à prendre ..
-

Nos astuces pour empêcher des chaussettes hautes de glisser
Il n’y a rien de pire que de porter des chaussettes hautes qui glissent. Heureusement, il y a quelques astuces à connaître pour maintenir vos chaussettes ..
-

Notre guide d’achat des NFT
Si vous aimez l’art numérique, vous pouvez peut-être devenir multimillionnaire en exploitant correctement le marché de la crypto et de la NFT. Avec une bonne ..
-

PC portable Dell 15 pouces : A quel prix peut-on l’acheter ?
Vous souhaitez acheter votre premier ordinateur portable ou vous devez en changer. Après avoir longuement réfléchi, votre choix s’est arrêté sur un modèle ..
-

Quel support Akilux acheter pour faire un panneau d’affichage ? publicitaire
Dans le cadre de votre travail ou bien un autre, il se peut que vous ayez besoin d’avoir recours à un panneau d’affichage dans une démarche publicitaire. ..
-
Comment faire briller le cuir de son canapé simili ? Découvrez nos conseils d’entretien !
Après de longues années de bons et loyaux services, votre mobilier de salon est désormais assez usé, et les assises se sont creusées avec le temps, le rendant ..
-

Comment nettoyer des vieux objets sans les abîmer ?
Vous avez un joli coffret en bois, ou une ancienne statuette qui commence à se détériorer ? Comment faire pour que ces objets ne partent pas directement à la poubelle ..
-

Comment utiliser un chiffon microfibre ?
Les chiffons en microfibres (parfois appelées serviettes en microfibres) sont l’un des outils les plus importants utilisés par les experts du ménage. Il est impossible ..
-

Comment utiliser la Terre de Sommières dans son nettoyage ?
Vous êtes à la recherche de nouveaux produits nettoyants pour faire le ménage dans votre maison ? Quitte à découvrir des nouveautés, pourquoi ne pas vous orienter ..
-

Comment trouver un moteur pour float tube ?
Avec de plus en plus de français qui se passionnent pour le monde de la pêche et de la navigation sur l’eau, autant le dire tout de suite : les équipements ..
-

Quel est le prix d’une formation data analyst à Nice ?
La formation data analyst à Nice est incontournable si vous souhaitez devenir Data analyst auprès d’une compagnie d’assurance, d’une banque, d’un grand ..
-

Quel est le meilleur maillot de bain menstruel 1 pièce ?
Les règles menstruelles font partie des nombreuses difficultés liées à l’existence d’une femme. En effet chaque mois ces dernières sont indisposées, ..
-
Comment utiliser un correcteur de faute d’orthographe et de grammaire ?
Vous avez tendance à faire beaucoup de fautes d’orthographe et vous souhaitez y remédier le plus possible lorsque vous êtes sur votre ordinateur ? Il est vrai ..
-
Comment trouver une chaise de bureau vintage industrielle ?
Il est important de créer une ambiance à son goût pour stimuler sa productivité et sa créativité dans son lieu de travail. Le choix éclairé des accessoires ..
-

Où acheter une chaise de salle a manger en osier ?
La chaise fabriquée en osier a connu un grand succès à une certaine époque. En effet, cette chaise se distingue par son design qui permet d’embellir parfaitement ..
-

Quel est le tarif d’une plaque funéraire musulmane ?
De manière générale, il est commun d’organiser un endroit de recueillement pour rendre hommage à une personne défunte. En effet cela donne l’occasion ..
-
Quel est le tarif d’une grenouillère pour adulte avec pied ?
Quel est le tarif d’une grenouillère pour adulte avec pied ? On trouve aujourd’hui des grenouillères non seulement pour bébé, mais aussi pour adulte. ..
-

Ou faire du canyoning ?
Bien choisir le site ou faire du canyoning De plus en plus de personnes s’intéressent à cette activité dans la nature qu’est le canyoning. En effet, que ce soit ..
-
Où trouver des avis sur la voyance par téléphone sérieuse ?
Avec le cout de la vie en constante augmentation, les virus inconnus à ce jour comme la COVID-19 et le réchauffement climatique, nous sommes de plus en plus de personnes ..
-

Comment choisir une assurance professionnelle pour la restauration ?
Quand on est propriétaire d’un restaurant, on gère de nombreuses choses. Ses employés, les aliments, la cuisine, le service, les clients… Et il y a donc ..
-

Comment faire estimer sa maison pour l’assurance ?
Avec une crise économique qui ne s’est jamais annoncée aussi difficile que cela, on constate tout de même que de plus en plus de personnes peuvent être ..
-

Comment trouver une bague en moissanite en or ?
C’est bientôt l’anniversaire de votre chérie, et vous avez envie de lui offrir un beau bijou. Vous comptez lui offrir une bague en or, avec une pierre ..
-

Quel est le tarif d’un anti-moustique pour bébé en pharmacie ?
Les moustiques sont un réel dérangement pour nous l’été. De plus, ceux-ci peuvent être très dangereux suivant leur race ainsi que le système immunitaire ..
-

Quel camping à Argeles sur Mer est avec une piscine couverte ?
Le camping est un endroit parfait pour passer des vacances entre amis pour pas très cher. En effet, les campings sont des endroits dans lesquels vous devez apporter ..
-

Où acheter une pièce pour smartphone ?
Vous rencontrez un problème technique avec votre smartphone, ou alors il ne fonctionne plus ? Depuis la mode des smartphones reconditionnés, la réparation est au goût ..
-

Pourquoi mon Iphone 8 ne charge plus ?
Les smartphones en général et plus particulièrement la marque Apple avec ses iPhone ont révolutionnés nos façons de vivre ces dernières années et il est très ..
-

Où acheter une bougie de fabrication française ?
Les bougies sont de parfaits accessoires qui peuvent non seulement sublimer une décoration, mais également amener une ambiance cocooning grâce à l’odeur ..
-

Quel est le prix d’un tirage photo en 20×20 ?
Vous souhaitez exposer vos photos de famille, de vacances ou de randonnée dans votre cadre de vie ? Cela est aujourd’hui possible en quelques clics grâce ..
-

Comment trouver une promo de forfait 5G ?
La 5G est en train de se démocratiser et de plus en plus de personnes désirent avoir un forfait équipé. En effet, grâce à la 5G, vous avez la possibilité ..
-

Comment régler un radiateur électrique à inertie ?
Il y a de nombreuses raisons pour lesquelles le fait de ne pas payer trop cher sa facture d’électricité est idéal, que ce soit au niveau économique ou au niveau ..
-

Où trouver des billets pour un train de prestige ?
Il existe diverses solutions que vous pouvez suivre pour effectuer une virée pour une destination fixe. Cependant, afin de profiter d’un voyage luxueux, vous ..
-

Comment choisir un poêle à bois de 10 kw ?
De plus en plus de personnes changent leur habitude de consommation en termes de chauffage pour le bois. Mais quels sont réellement les avantages d’un poêle ..
-

Comment faire un crédit rapide de 500 euros ?
Durant votre vie vous allez très certainement vouloir réaliser des grands projets, qui vont sans doute bouleverser votre quotidien. Cela peut être par exemple ..
-
Pourquoi les quincailleries sont importantes sur les fenêtres PVC ?
Même si vos fenêtres en PVC sont neuves, vous n’êtes pas à l’abri, un jour ou l’autre, de rencontrer un problème. Il convient donc d’entretenir vos menuiseries ..
-

Comment acheter des pièces pour son tracteur agricole ?
Lorsque vous travaillez dans le secteur agricole, vous savez à quel point vous devez avoir du matériel de qualité mais aussi des machines pour que vous puissiez ..
-

Quel est le tarif d’une agence de stratégie digitale en Ile-de-France ?
Le marketing digital est un outil essentiel pour votre entreprise. Il favorise l’accroissement des activités et le bon fonctionnement de votre société. ..
-

Quel est le meilleur mobilier urbain mobile ?
L’aménagement du territoire est l’un des enjeux majeurs de la politique locale en France. Améliorer les espaces de vie pour faciliter les conditions ..
-

Où trouver un maillot de bain pour femme gainant ?
Le maillot de bain met en valeur les courbes féminines. C’est un vêtement confortable proposé dans différentes matières par de nombreux vendeurs. L’un des modèles ..
-

Quel est le meilleur menu de chrononutrition pour une personne de 1m65 ?
A l’instar de bon nombre de gens, le régime va sûrement être un passage obligé durant votre vie. Et ce pour plusieurs raisons ; que vous souhaitiez par exemple ..
-

Quels sont les meilleurs outils de test fonctionnel ?
Pendant les phases de tests logiciels, on distingue deux grandes catégories de tests. Les tests dit non fonctionnels, comme le test de robustesse, de compatibilité ..
-
Quels sont les indicateurs sociaux d’une entreprise ?
Vous êtes à la tête d’une entreprise de plus de 300 salariés ? Vous avez très certainement entendu parler du bilan social et des indicateurs sociaux si tel est le cas. ..